The Cloud8 Platform continues to evolve! We arrive with another update on the releases of recent weeks. There’s news in the Scheduler , in Security and much more. Here are the main ones, most requested by our customers and users.
Workflow with script execution and EC2 Command
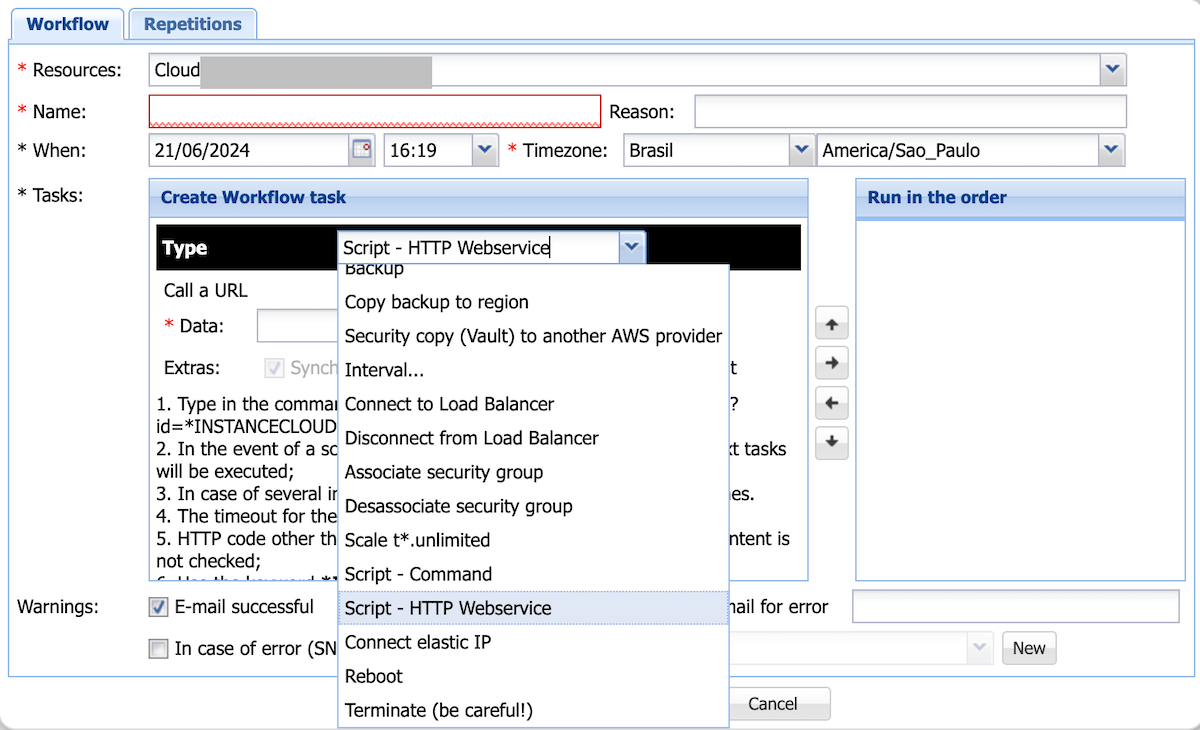
We implement the script execution task in our Scheduler .
For now, it is possible to run 2 types of scripts:
- HTTP/HTTPS call . Wrap a script through an HTTP call. Cloud8 will wait 60 seconds and send the response of this call. If the status returned is different from 2xx , it is considered an error and you will be notified. To protect this webservice , we suggest something like passing a code in the call and validating it within the script.
Example: http://yoursite/yourscript?code=abcxyz - EC2 Command . This is the AWS recommended way to run scripts . You do not need to pass credentials (passwords or digital certificates). You must install an AWS application if the environment is Linux , have an associated IAM Instance Profile and an exit to the internet. See the full requirements .
Remember that running scripts is valid for both Linux and Windows . In the case of EC2 Command , AWS already provides a series of pre-registered commands ( shell , powershell ) that you can use.
Usage suggestions
- Execute maintenance scripts , reducing the need for access and documenting changes in the audit: applying patches , security checks, executing recipes , reports, installing applications, etc.
- Schedules : after starting or upgrading / downgrading a server, run script to check if everything is working correctly: Database up? Is disk space OK? Are all services working?
- In the development environment , integrate the start of the server with the execution of a script that copies the production database and removes critical fields such as passwords, personal data, etc.;
- Before shutting down , do a ‘clean’ shutdown , stopping services, database, notifying other applications, etc.;
- Before making a backup , ‘ freeze ‘ the filesystems , make the backup and then do an ‘ unfreeze ‘ – improves the consistency of the snapshots ;
- Monthly/weekly maintenance of security patch application ;
- Manipulate some AWS service like copying files to S3, etc.
Workflow: Scale concurrent services with Fargate

It is now possible to turn off one or more ECS services at once or all at once (previously it was necessary to create a schedule for each service).
All ECS tasks support these configurations:
- Scale / Shutdown Service
- Change capacity provider
- Change task definition (an “ upgrade / downgrade ”) of tasks
Remembering that for containers linked to ASG , scheduling can be done by the “ Apps (Auto Scaling) ” components, defining the min / max / desired values .
Security: IAM Instance Profile Monitoring
We are always concerned about improving the security of your cloud environment . We have added another component to IAM monitoring: IAM Instance Profile .
The IAM Instance Profile is a kind of ‘ Role ‘ that is directly linked to servers. When you create a server, you can associate it with an Instance Profile . This way, this server incorporates the Role ‘s permissions and it is not necessary to have hardcoded local credentials . As a best practice, it is recommended to create servers associated with an Instance Profile – even if it does not have any permissions. In the future, if you need to run scripts on this server, you can use EC2 Command , which is the most recommended way.
We have also flagged in the list of servers those that have an Instance Profile and the policy details in the IAM report !
Why is this monitoring important?
If you have servers associated with an Instance Profile (remember that BeanStalk and OpsWorks are automatically linked to one) and they are compromised in some way, the hacker / (ex-)employee can execute AWS API calls without needing keys. Depending on the permissions they have, this can put your infrastructure at risk. It is important to know if the permissions have been changed and if the servers have ‘too high’ permissions – usually administrative policies with low impact are set (such as executing pre-registered EC2 Command ).
Support for a new India region
As usual, we automatically support the new India/Mumbai region . We’ve included all the features that are already present in the other regions!
More news
We continue to implement new improvements to all features of the Cloud8 Platform.
- Infrastructure alert : We include the server start date – this improves diagnostics by eliminating false positives;
- Scheduler : Improvement in the usability of creating Workflow tasks ;
- RDS Aurora : Handling more alert scenarios (e.g. failover completion );
- Correction : Improvement in checking custom credentials to send email when registering a logo;
- Fix : Exporting cost and usage graphs to CSV could sometimes show the next day’s usage instead of the current day’s usage. This is no longer the case.
Questions, criticisms, suggestions? We are always open and grateful to your suggestions. Contact!