To integrate an Oracle Cloud (OCI) account with the Cloud8 Platform, you’ll need to provide access credentials in your account settings with us. Follow the tutorial below to complete this setup.
Setting OCI Access Credentials #
We suggest you open a notepad and be ready to write down the following information:
- CONFIGURATION FILE PREVIEW (PASSO 1)
- GROUP NAME ( STEP 2 )
- PEM ( STEP 2 )
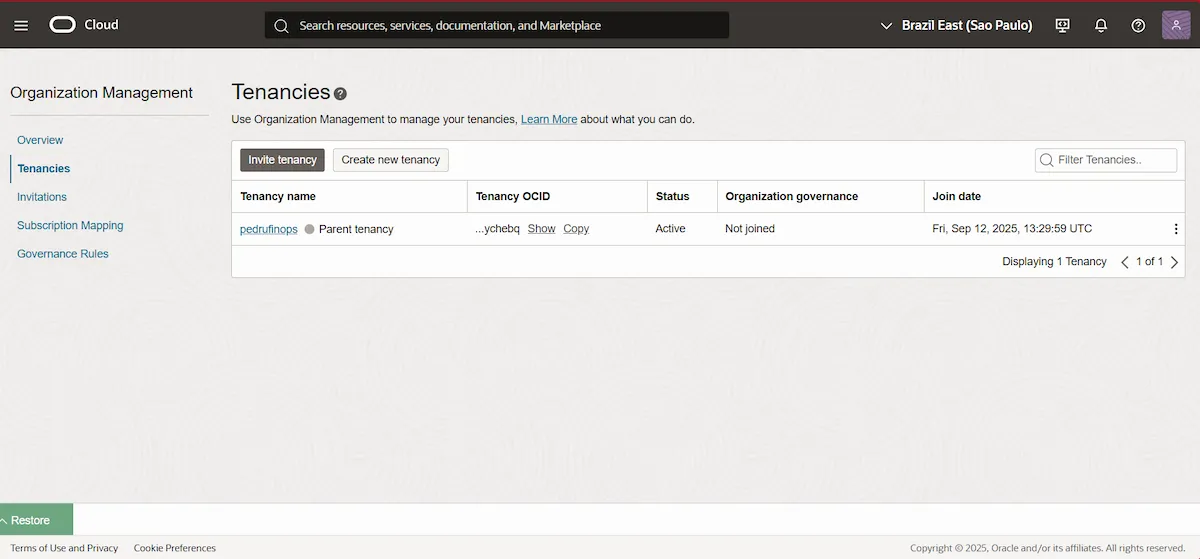
First, we suggest checking the OCI Organization structure . In the top search bar, search for Tenancies . Configuration should first be performed in the Organization ‘s Parent tenancy .
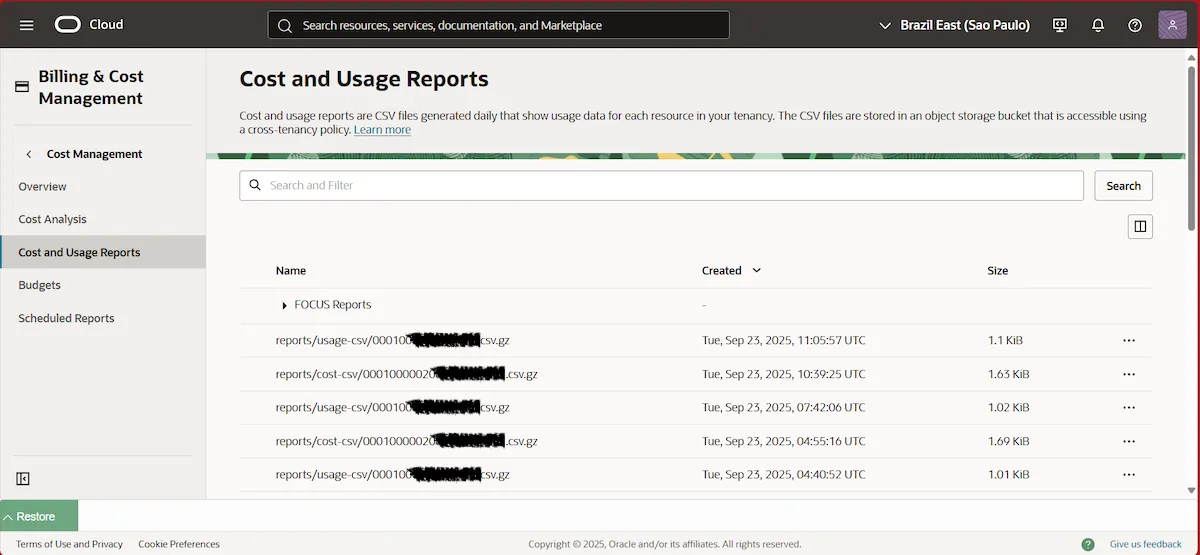
Then, validate the existence of CUR ( Cost and Usage Report ) by searching for “ Cost and Usage Reports ” in the top search bar.
Step 1 – Creating a user #
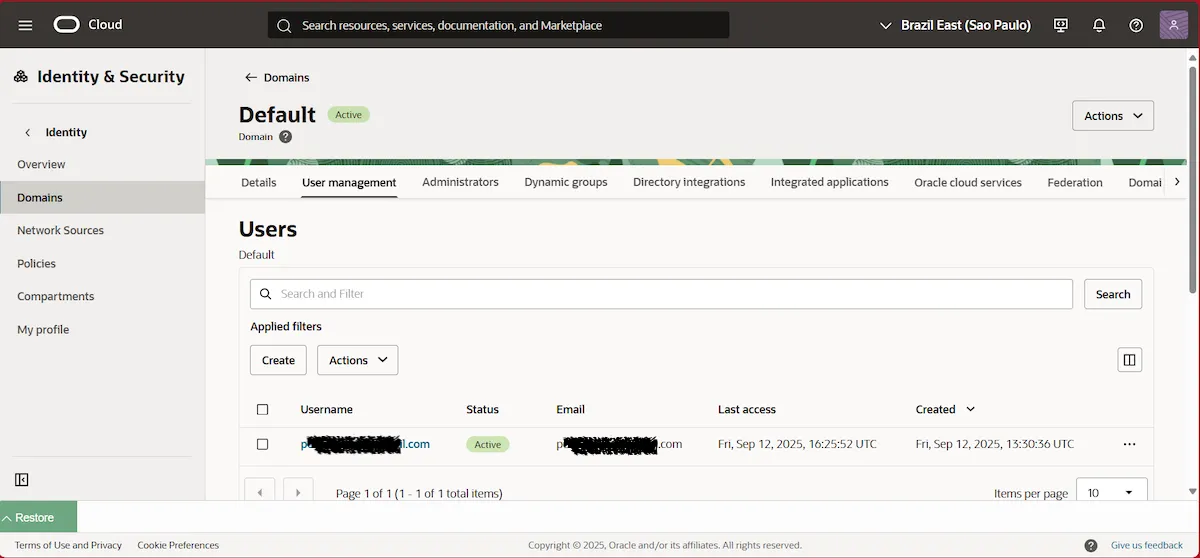
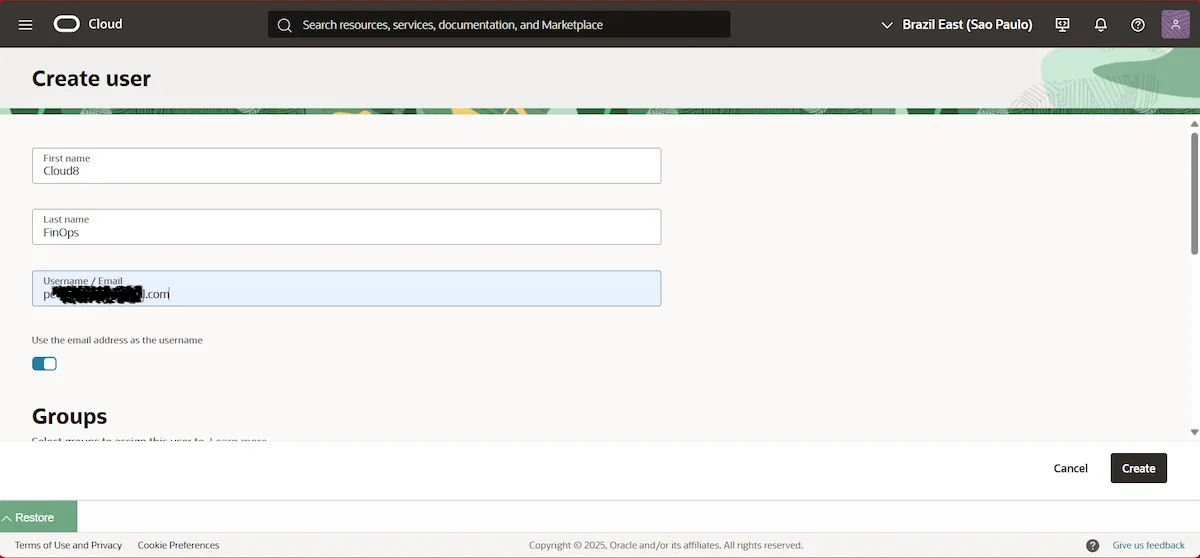
Then, in the top search bar, search for Domains and select the Default domain . In the User management tab , find Users and click Create . We suggest using the username Cloud8.
Set your First name , Last name , and Username/Email. We recommend using an email address that allows you to reset your information if necessary. Then click Create .
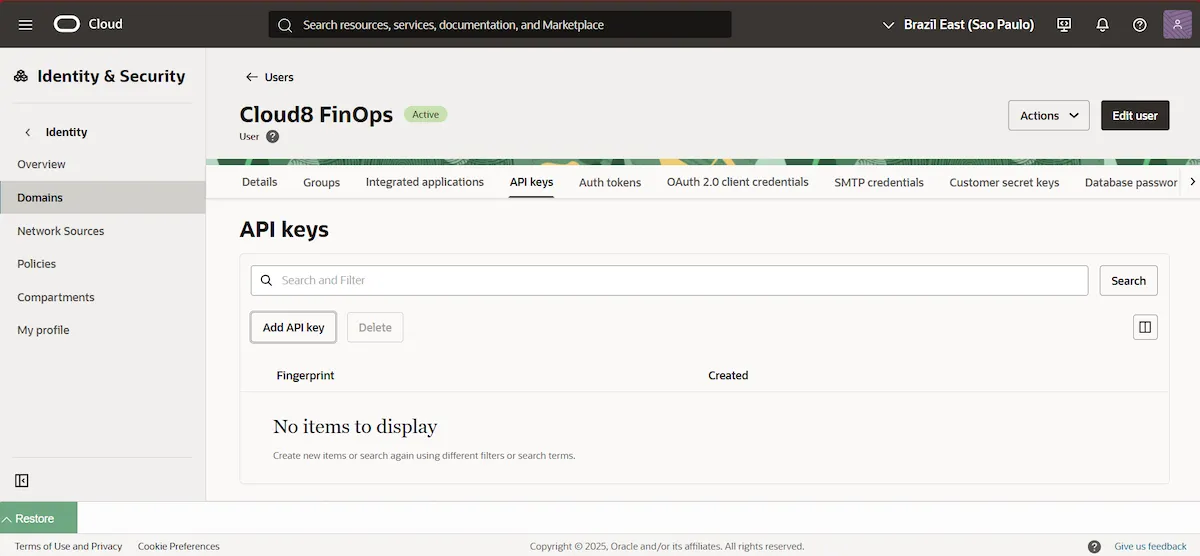
Then, create an API Key for the created user by clicking on the API Key tab and then on Add API key .
Select the Generate API key pair option , and download the private key and public key .
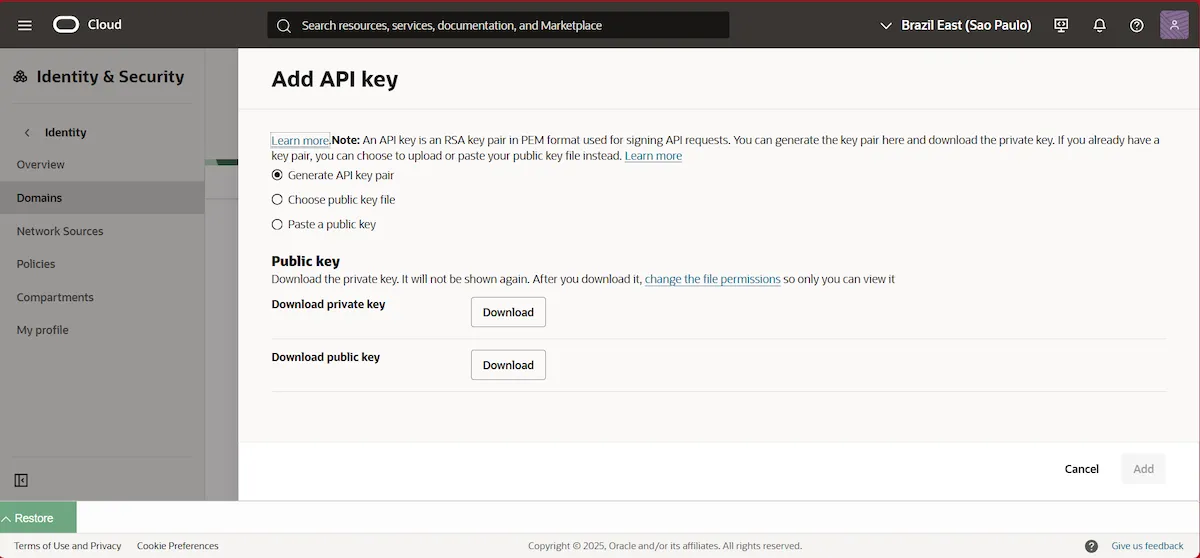
We recommend storing the downloaded API keys in a secure repository or vault in case you need to use them later. Finally, click Add .
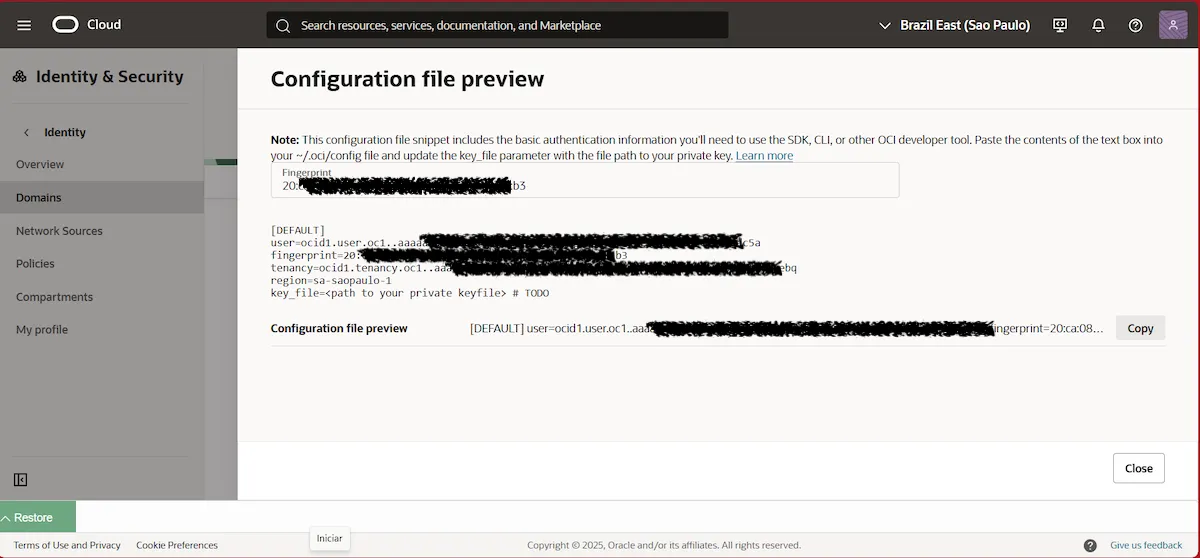
Copy the contents of the Configuration file preview and save it to a notepad.
Step 2 – Create an Access Group #
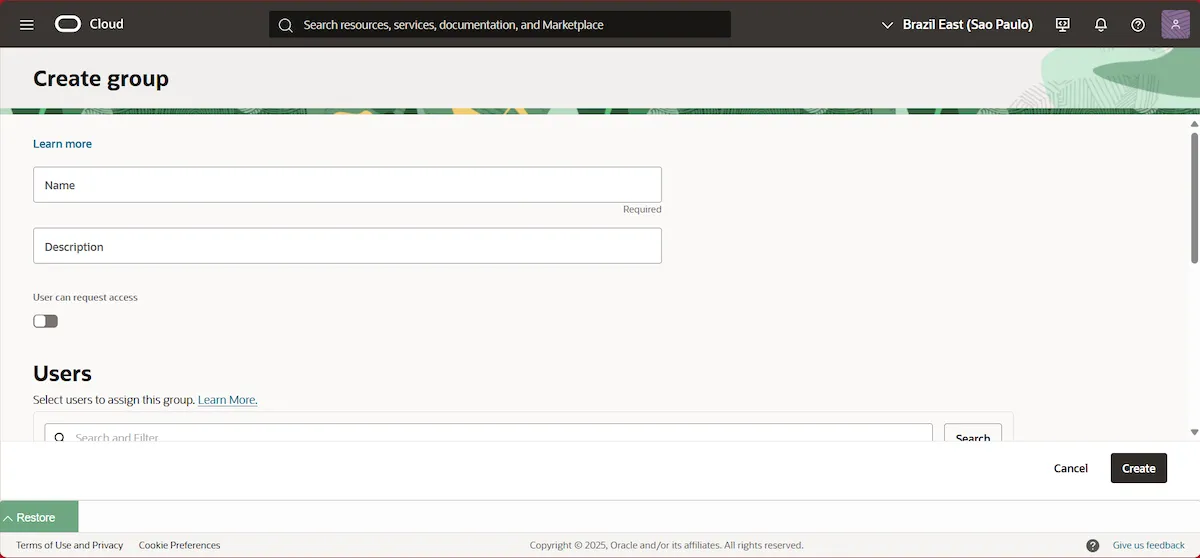
Return to Domains , select the Default domain again, and in the User Management tab , scroll down until you find Groups . Click Create group .
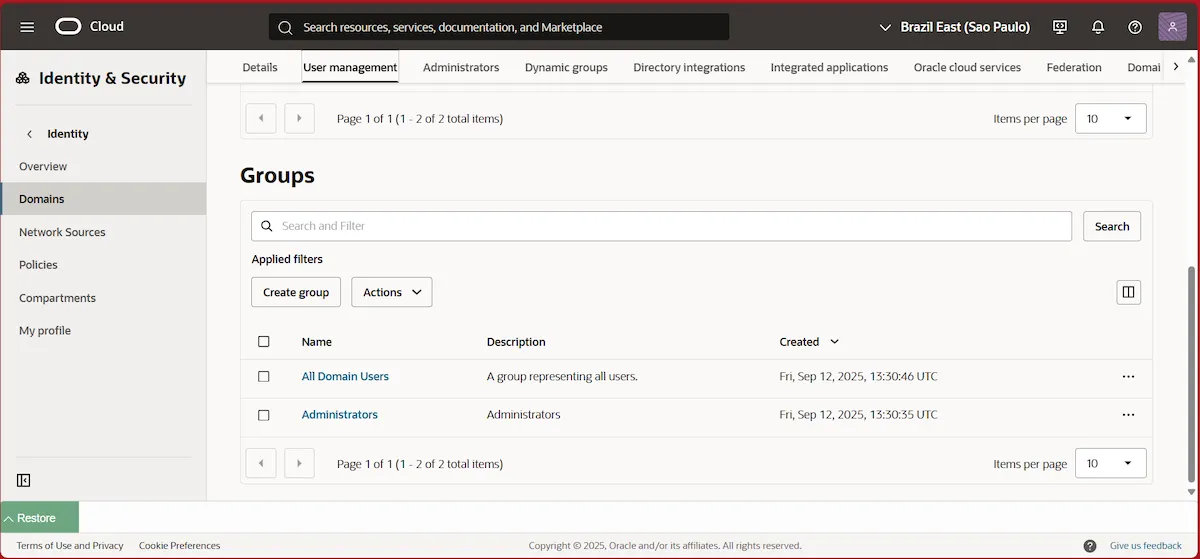
Select a name for the group and user you created in the previous step. Then click Create . Write down the group’s Name in notepad for later use.
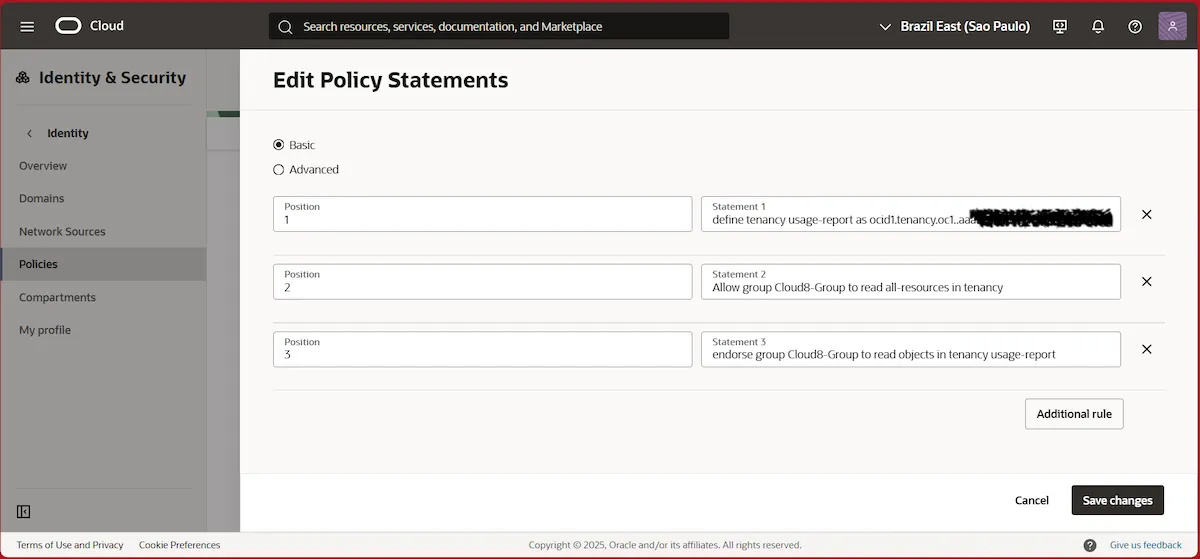
Step 3 – Create an Access Policy #
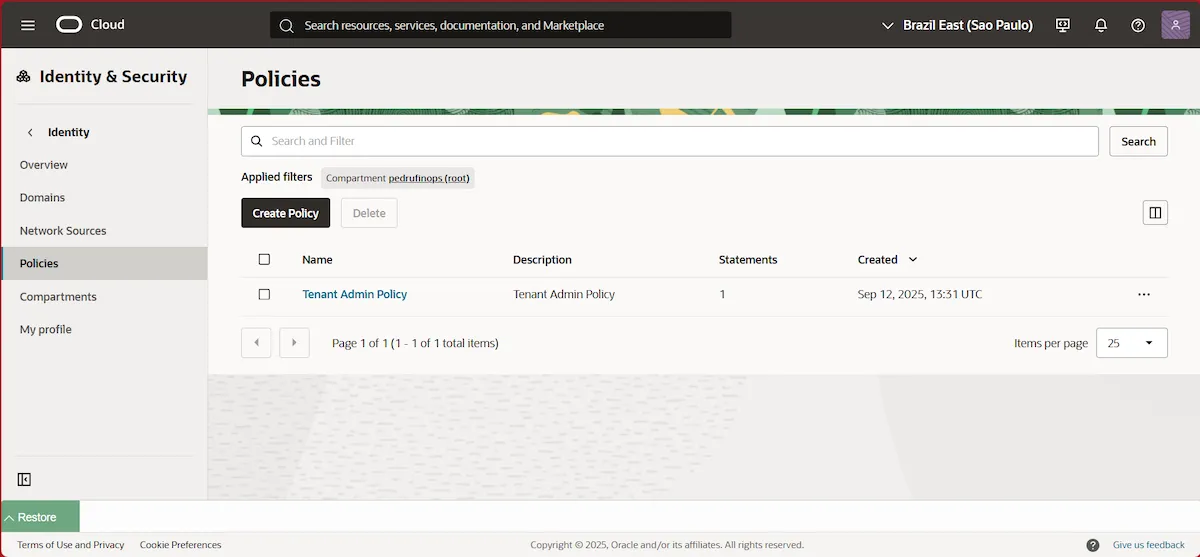
In the left side menu, select Policies , and click Create Policy in the root compartment .
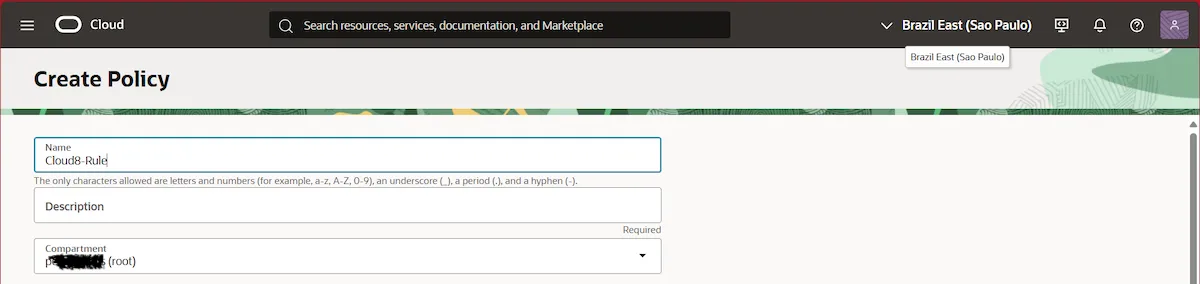
Set a name for the policy and select the Root Compartment .
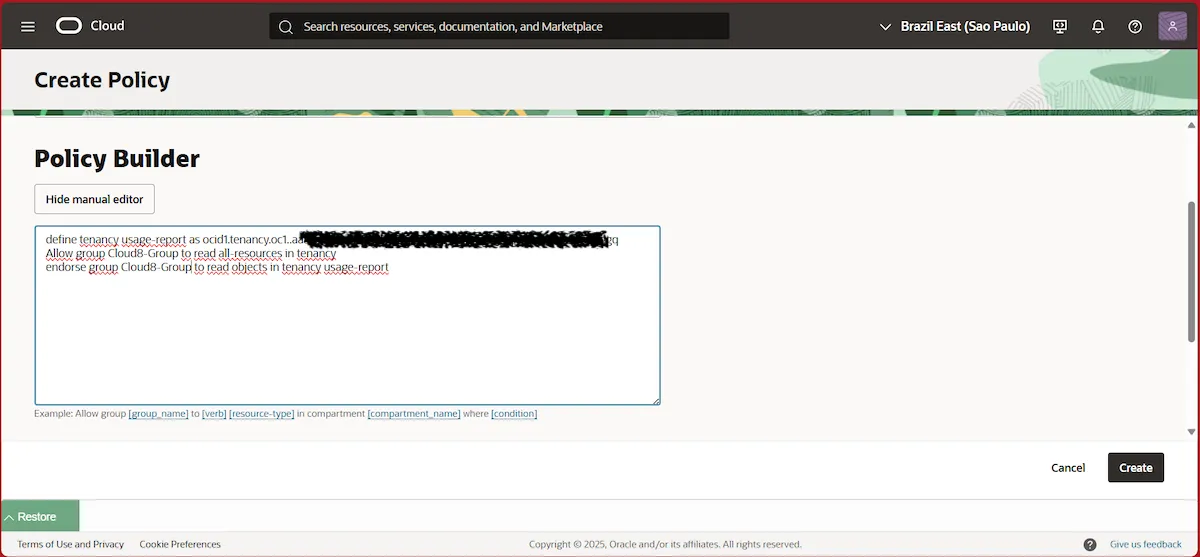
In the Policy Builder section , click Show manual editor . Then, copy the policy definition below:
define tenancy usage-report as ocid1.tenancy.oc1..aaaaaaaaned4fkpkisbwjlr56u7cj63lf3wffbilvqknstgtvzub7vhqkggq
Allow group __MYGROUP__ to read all-resources in tenancy
endorse group __MYGROUP__ to read objects in tenancy usage-reportIMPORTANT: Do not change the tenancy code above as it is Oracle default.
Replace __MYGROUP__ with the name of the Group that was created in the previous step, then click Create .
Step 4 – Configuring access credentials on Cloud8 #
In the left-hand side menu, select “ Providers .” Click “ New ” and fill in the required fields with the data generated in the previous steps.
- Provider name : The name that will be used to identify the provider in Cloud8.
- Timezone : local time standard that will be used.
- Language : default language.
- Default location : Choose the most popular or most used location for your account, we will scan all regions and zones anyway.
- User : Available in CONFIGURATION FILE PREVIEW ( Step 1 )
- Tenancy : Available in CONFIGURATION FILE PREVIEW ( Step 1 )
- Fingerprint : Available in CONFIGURATION FILE PREVIEW ( Step 1 )
- PEM : theuser’s private key created in Step 1
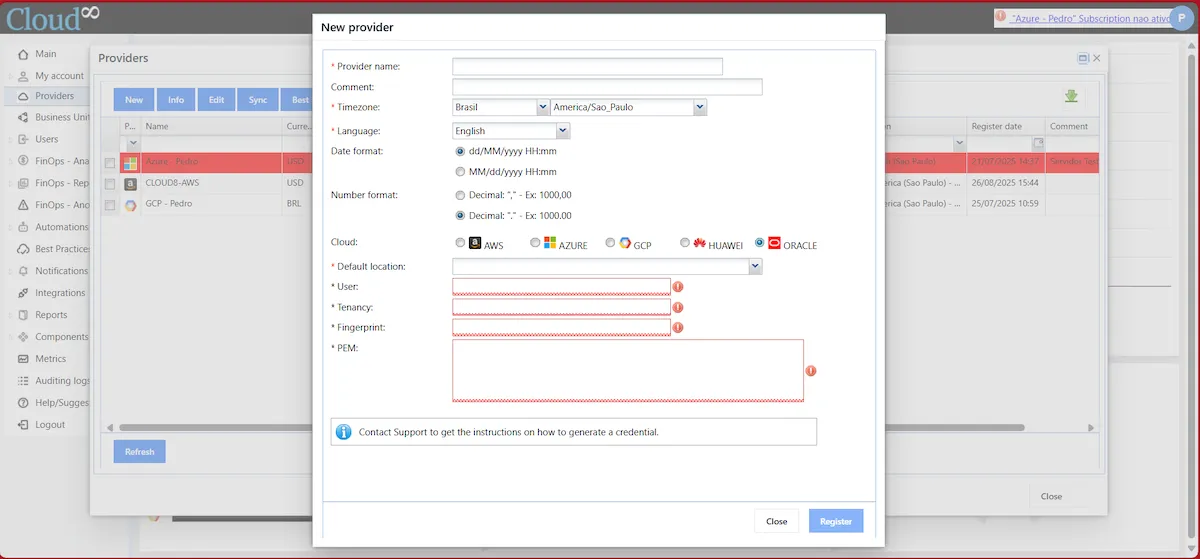
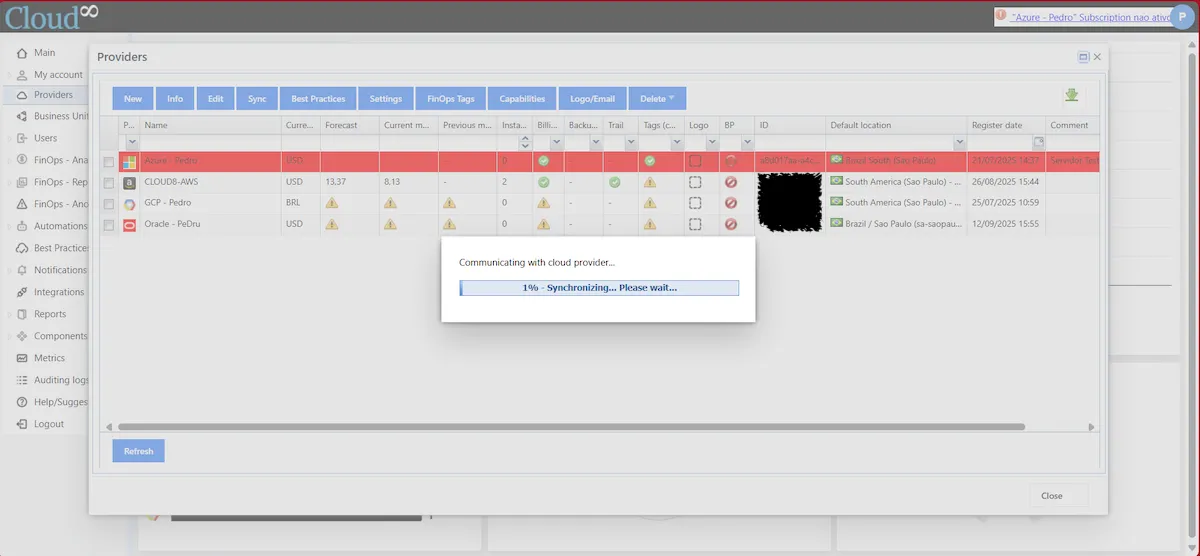
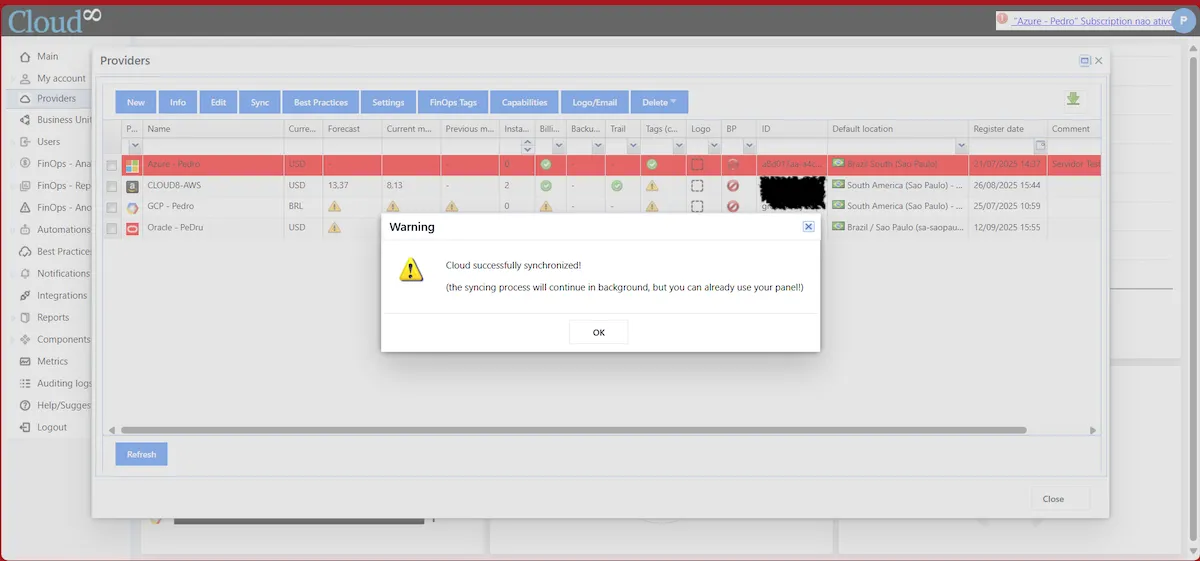
Click Register , and wait for the Synchronization to complete.
Specific permissions for automations #
Some Cloud8 modules require specific permissions to be granted. Add them by editing the Statements of the created Policy and clicking Edit Policy .
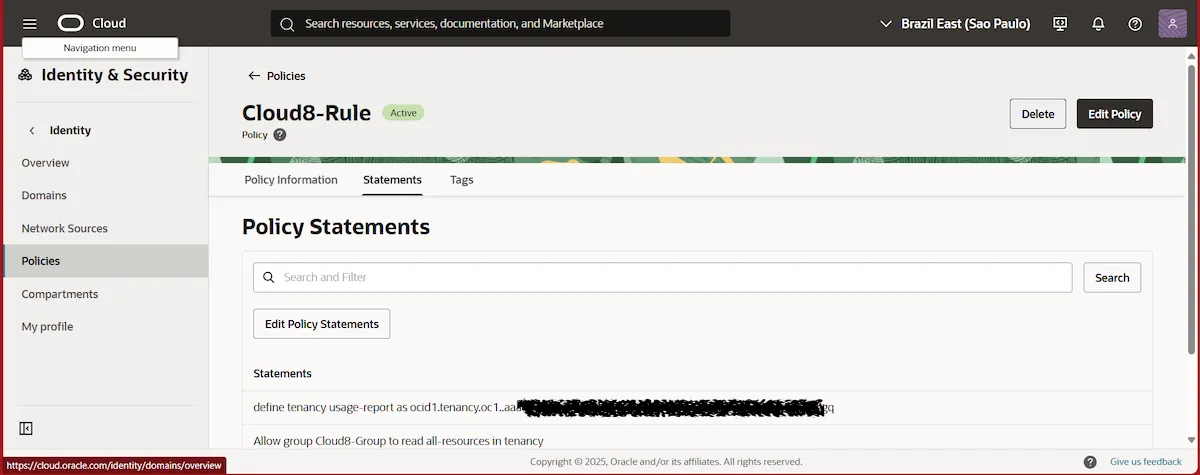
Click Additional rule , add the necessary permissions, and click Save changes .
Turn On/Off/Upgrade/Downgrade Instances #
Allow group __MYGROUP__ to manage instance-family in tenancy where any {request.permission='INSTANCE_POWER_ACTIONS', request.permission='INSTANCE_UPDATE'}Backup #
Allow group __MYGROUP__ to manage volume-family in tenancy where any {request.permission='VOLUME_BACKUP_CREATE', request.permission='VOLUME_WRITE', request.permission='VOLUME_UPDATE', request.permission='VOLUME_BACKUP_DELETE', request.permission='BOOT_VOLUME_BACKUP_CREATE', request.permission='BOOT_VOLUME_BACKUP_DELETE', request.permission='VOLUME_GROUP_BACKUP_CREATE', request.permission='VOLUME_GROUP_BACKUP_DELETE'}MySQL – On / Off #
Allow group __MYGROUP__ to manage mysql-family in tenancy where any {request.permission='MYSQL_INSTANCE_USE', requesAllow group __MYGROUP__ to manage database-family in tenancy where any {request.permission='DB_NODE_POWER_ACTIONS', request.permission='DB_BACKUP_DELETE', request.permission='DB_BACKUP_CREATE'}DbSystems – On / Off #
Allow group __MYGROUP__ to manage database-family in tenancy where any {request.permission='DB_NODE_POWER_ACTIONS', request.permission='DB_BACKUP_DELETE', request.permission='DB_BACKUP_CREATE'}Manage Tags #
Allow group __MYGROUP__ to use tag-namespaces in tenancyOKE Cluster NodePools – Power On/Off #
Allow group __MYGROUP__ to use subnets in tenancy
Allow group __MYGROUP__ to use vnics in tenancy
Allow group __MYGROUP__ to manage instance-family in tenancyIMPORTANT:
1 – The ‘manage instance-family’ permission is required for NodePools .
2 – To avoid mixing with non- Kubernetes instances , we recommend using ‘in compartment <compartment-name>’ instead of the entire tenancy.
Instance Pools – On / Off / Scale (zero / +1) #
Allow group __MYGROUP__ to use instance-pools in tenancy
Allow group __MYGROUP__ to manage compute-management-family in tenancyNOTE: The ‘compute-management-family’ permission is required to scale Instance Pools .
Auto Scaling Groups Policy #
Allow group __MYGROUP__ to use auto-scaling-configurations in tenancy
Allow group __MYGROUP__ to manage auto-scaling-configurations in tenancyExadata – Scaling the number of OCPUs #
Allow group __MYGROUP__ to manage cloud-vmcluster in compartment <your_compartment_name> where any {request.permission='CLOUD_VM_CLUSTER_UPDATE', request.permission='CLOUD_EXADATA_INFRASTRUCTURE_UPDATE'}Autonomous DB – On/Off #
Allow group __MYGROUP__ to use autonomous-databases in compartment <your_compartment_name> where any {request.permission='AUTONOMOUS_DATABASE_UPDATE'}Setting up FinOps Analytics on Cloud8 #
FinOps Analytics is configured through a Cost and Usage Report configured with the Oracle provider. This configuration is performed automatically in the previous step, through the configured Access Policy .
Enabling Best Practices on Cloud8 #
Once FinOps Analytics configuration is complete and data is synchronized to Cloud8, you can enable the Best Practices feature in Cloud8 .
Best Practices is an advanced advisor that combines over 1,000 unique security, backup, compliance, and cost reduction rules for AWS, Azure, GCP, and OCI with flexible alerting via Teams, Slack, or email.
In the Cloud8 side menu, select Providers . Select the desired provider and click “ Best Practices .”
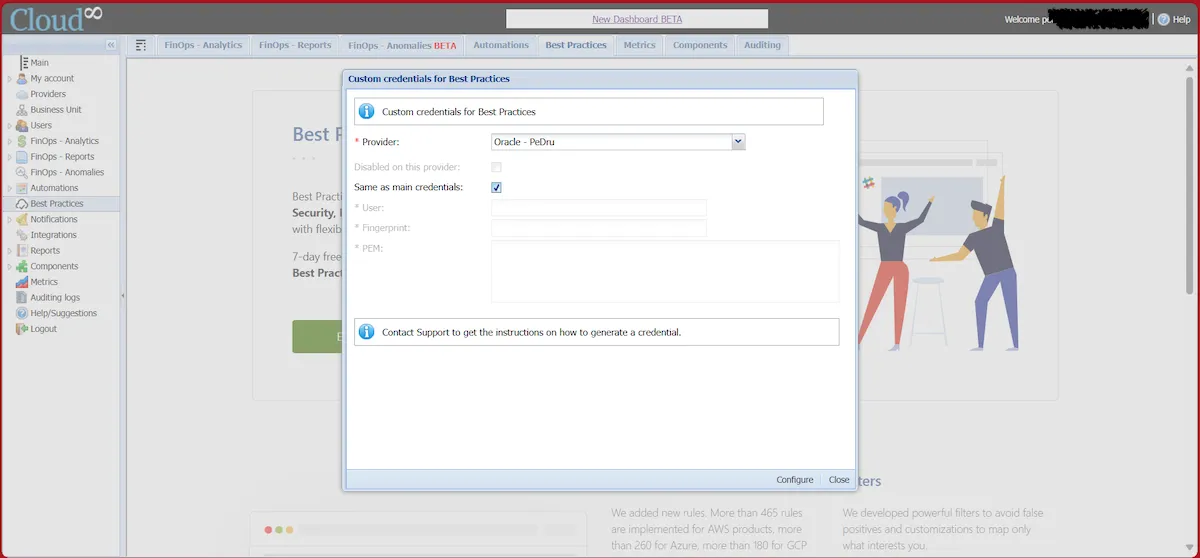
You must select the providers on which you want to enable the functionality, and to do so, uncheck the “ Disabled on this provider ” checkbox and select the “ Same as main credentials ” option.
Then click on “ Configure ”.
IMPORTANT: After enabling FinOps Analytics , you will need to wait at least 24 hours to enable the Best Practices functionality .



